PCI and PAN Scan
The PCI and PAN Scan Report incorporates both the PCI DSS Requirements and CVSS Scored results for the selected device.
Device details
Shows the assessment completion time, host name, IP address, and platform. To export the report, select. the PDF version button.
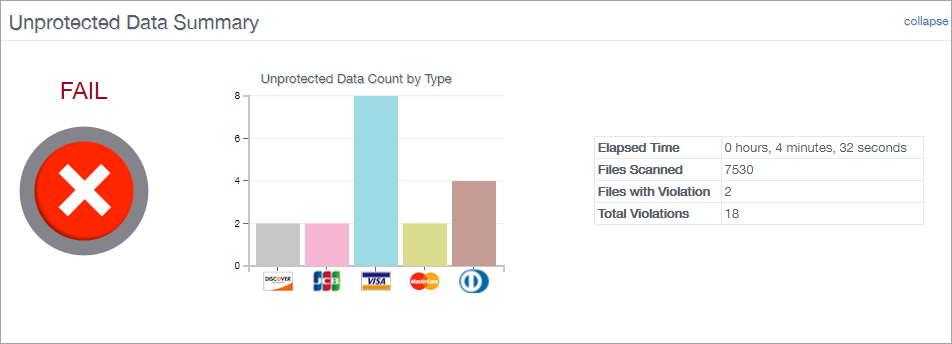
Unprotected Data Summary
Contains a graph displaying the Unprotected Data type count. For example credit cards, dates of birth, driver licenses, social security numbers etc. Along with how long the scan took to complete, the number of files that were scanned, the number of files that contained a violation, the total number of unique violations.
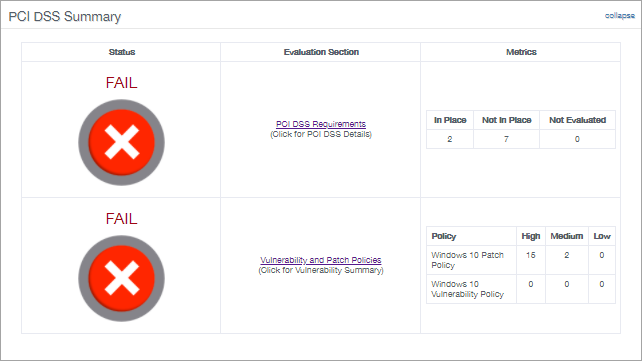
PCI DSS Summary
Displays the status as either a Pass or Fail for the PCI DSS Requirements and the Vulnerability and Patch Polices.
The PCI DSS Requirements are available when clicking the link to open the PCI DSS Details section and the metrics are classed as In Place (Passed), Not In Place (Failed) or Not Evaluated (skipped).
The Vulnerability patch policy and vulnerability checks are derived from the Security scan and show the severity of the vulnerability, (high, medium or low) based on the CVSS score.
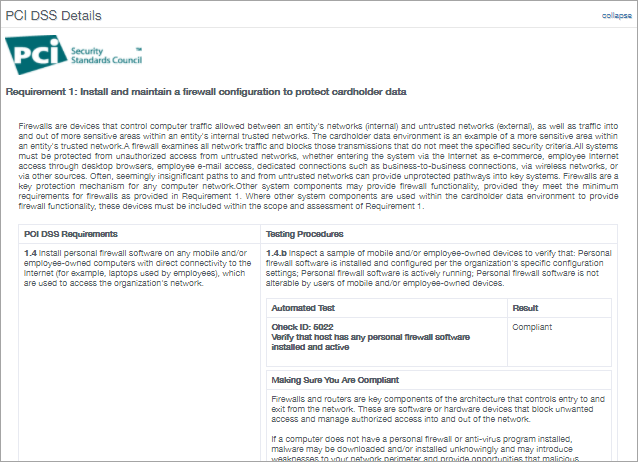
PCI DSS Details
Lists the PCI DSS Requirements from the Security Standards Council to find at risk data. Each entry contains the requirement and details. The testing procedure and Automated Test result, Compliant or Not Compliant.
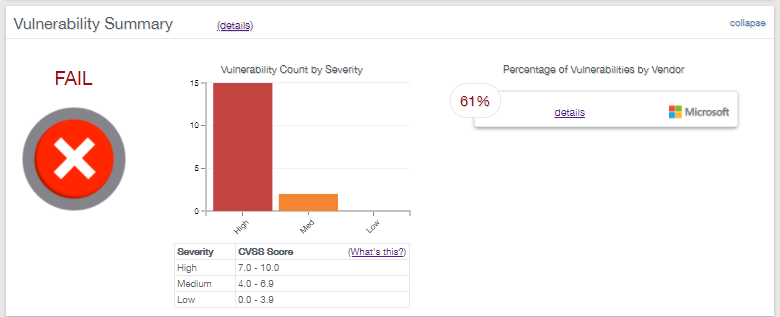
Vulnerability Summary
The Vulnerability Summary graph shows the vulnerability count by severity based on the Common Vulnerability Scoring System (CVSS) with each vulnerability assigned a severity of High, Medium or Low and percentage of vulnerabilities by vendor.
To break down this information click, on the details links to take you to the "Vulnerability Details" sections.
Details about Scoring
A vulnerability with a High level of severity will fail PCI compliance whereas vulnerabilities with Medium or Low severity levels will generally pass PCI compliance.
- High: 7.0 - 10.0
- Medium: 4.0 - 6.9
- Low: 0.0 - 3.9
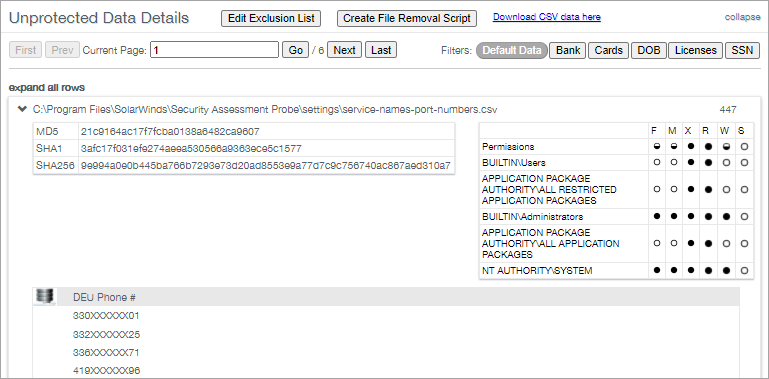
Unprotected Data Details
Lists the discovered files that contain unprotected data. Use the filters at the top of the section to focus on particular data types. For example, Bank details, Cards, Date of Birth, Licenses and Social Security numbers. Note, these filters only apply to the current page and are not retained between sessions.
Expand each entry to view additional information or expand all rows.
When expanded, the entry shows the file hash as MD5, SHA1 and SHA256. All user groups who have access to the file. A masked list of violations found in the file. No unmasked data leaves the scanned system.
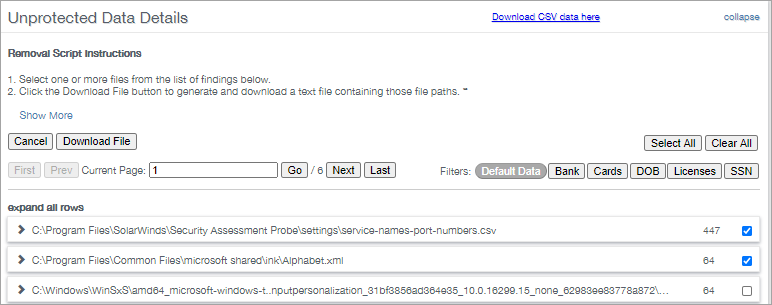
You also have the option to generate a batch file to run on the computer and permanently delete the files. Click on Create File Removal Script, tick the boxes against the entries to delete then click Download File.
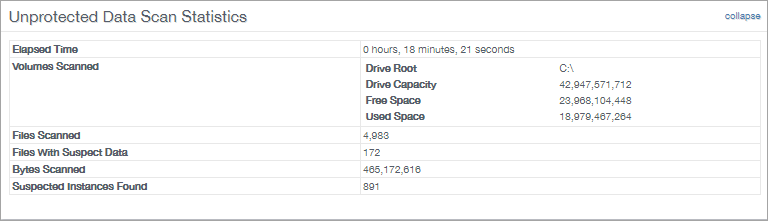
Unprotected Data Scan Statistics
This section displays the time it took to run the scan, volumes scanned, number of files scanned, number of files with suspect data, suspected instances found etc.
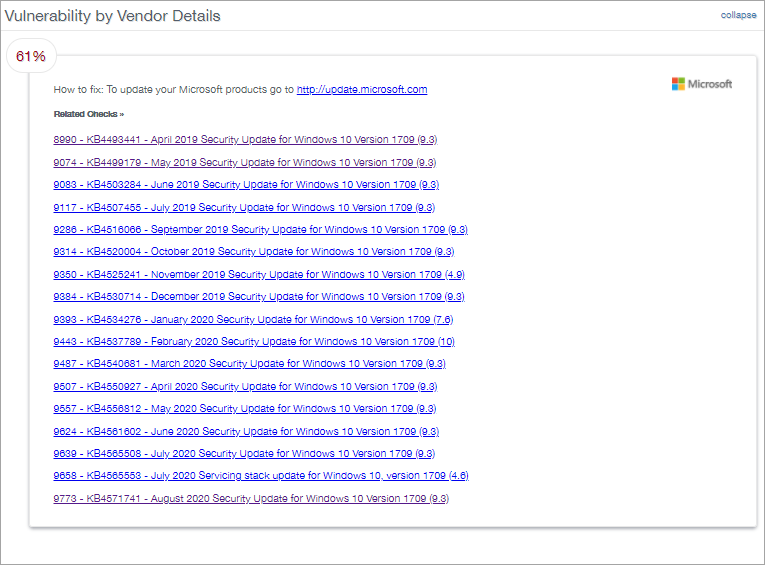
Vulnerability by Vendor Details
Lists the vulnerabilities discovered by vendor click on a vulnerability in this section to go to its entry in the Vulnerability Details section. This list details of the discovered vulnerabilities along with links to external sites that with instructions on how to alleviate the issue.
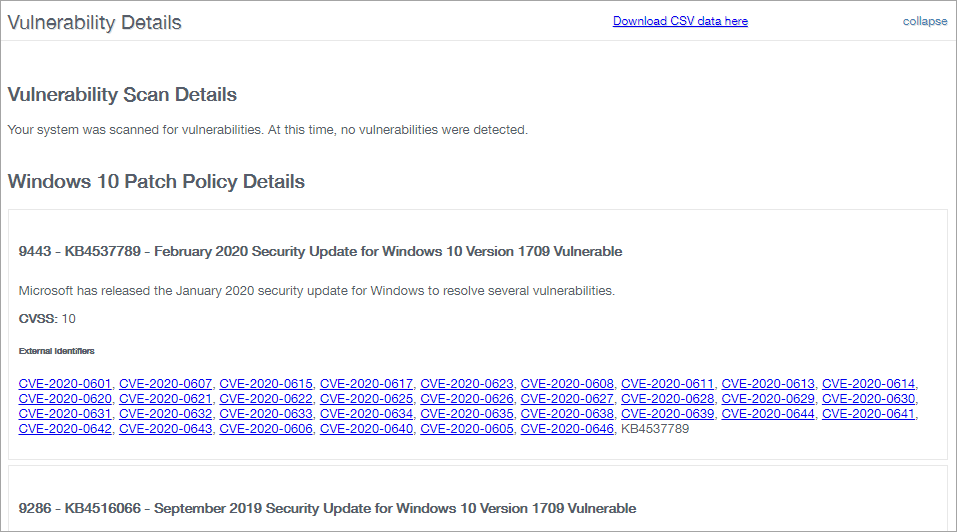
Vulnerability Details
List details of the discovered vulnerabilities along with links to external sites with instructions on how to alleviate the issue.
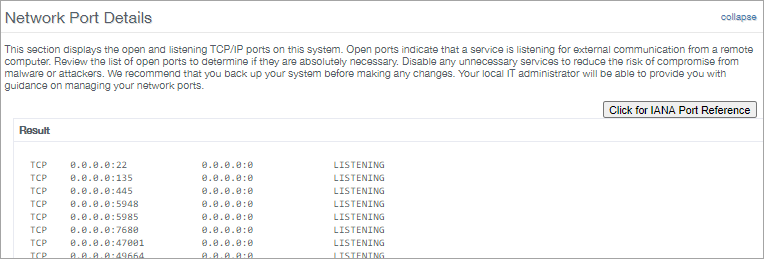
Network Port Details
Displays the listening TCP/IP ports on your system. These listening ports indicate that a service is listening for external communication from a remote computer.
From here you can review the list of open ports, determine if they are required and disable any unnecessary services to reduce the exposure to compromise from malware or attackers.
We have also included a button to open the Internet Assigned Numbers Authority at the service name and port numbers page.
Please note, we are not responsible for the content of external sites.
What do you want to do?