Most bad-actors try to trick email users via impersonation - pretending to be another person or company. To do this, they use sophisticated techniques to craft email attacks.
Display Name Spoofing
A spammer will often 'fake' the display name in an email while actually leaving the from address alone. They do this in the hopes of pretending to look and sound like it's a message from a known sender, while putting in minimal effort.
This type of spoofing is also known as Business Email Compromise (BEC), Whale phishing or VIP/CEO fraud and can be quite common.
Example:
From: "Dave-CEO" <pinkfruit@gmail.com> Sender: "Pinky" <pinkfruit@gmail.com> To: "Alice-Finance Boss" <alice@legitimate-demo-domain.invalid>
For messages such as this, you will see in Mail Assure that the Sender and From addresses are the same, but the name displayed under From has been changed. This is what can be seen in Mail Assure:
From Address Spoofing
Many phishers will use a fake From address as the spoofing option as this is what appears in your mail client, and can be easy to miss when looking at a message quickly.
Example:
From: "Paypal Support" <paypal@fake-pay-pal.com> Sender: "XYZ-2KF" <xyz-2kf@spammer-domain.com> To: "Alice-Finance Boss" <alice@legitimate-demo-domain.invalid>
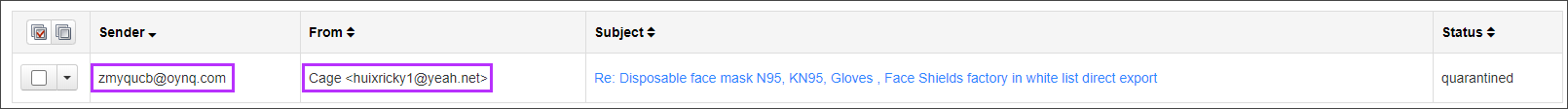
The easiest way to see that the address has been spoofed is by checking in Mail Assure's log search and viewing both the Sender and From columns, or checking the message headers and noting the differences between the Sender and From headers. Here is an example of what can be seen in Mail Assure when a From address is spoofed:
For full details on how to stop impersonation, see the Advanced Block list Filtering Rule page and Advanced Filtering Rule Examples and Quick Reference page for full details.