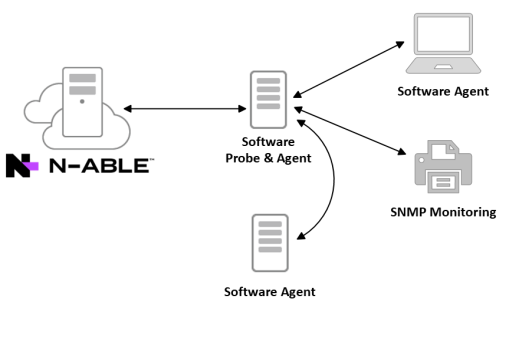
Architectural overview
To manage your devices N-able N-central relies on software probes and agents.
The probe, typically installed on an available Windows server, is responsible for your network equipment including routers, firewalls, switches and printers. Probes provide monitoring and management services for devices on that private network, leveraging industry standard protocols such as WMI, SNMP, ODBC, and others.
An agent is an additional software component that may be installed on a Microsoft, macOS, or Linux host device to gather data specific to that local device. Agents are typically installed on all Windows devices to provide full monitoring and management regardless of the logical placement of that device on the Internet.
In a workgroup environment, you will be able to install a Customer or Site specific software probe, and manually install your software agents on each of your managed systems. As you install agents, the devices will automatically be imported into N-able N-central. A quick discovery with your probe will also find and import your network devices.
Probe and agent communications
Probes and agents communicate with the N-able N-central server using similar architecture and methods. The probes and agents leverage client-side initiated communications, where all data communications begin with an outbound call from the agent or probe.
As a direct result of this architecture, there is no public IP address or port forwarding required from the Internet to the devices running the probes or agents. The outbound communications from the agents to the N-able N-central server are based on SOAP and XMPP, and are transmitted using the HTTP or HTTPS protocols on the standard web ports. The nature of these communications allows for the support of standard proxies on the local network.
After the outbound session is established, the agent receives a session ID that is used to identify that session and it persists until the session is closed. The agents and probes will open a second (asynchronous) signaling channel leveraging the XMPP protocol on port 80/443 that is persistent to allow the N-able N-central server to signal the probes and agents when actions are necessary, such as to initiate a remote control session. In cases where the XMPP session is terminated abnormally, for example, by a firewall cleaning open sessions, the agent will re-create the session automatically.
N-able N-central leverages the XMPP based communications for control purposes only, not for the transmission of monitored data. As an additional measure, the XMPP protocol can be turned off for individual devices or globally, however, this is not recommended as this will increase system load and will cause latency on certain N-able N-central features.
By default, the N-able N-central agent, probe, and XMPP-based communications use HTTPS with the data encrypted using TLS and the strongest cipher suite supported by both the client and the server.
The N-able N-central probe also acts as a cache location for software installation files such as the agent, AV Defender, Backup Manager, and Windows Patches. Agents communicate with the probe over TCP 10004 using the .NET remote communication protocol.
N-able N-central server
The N-able N-central server is the "brains" of the system and contains a number of components including the broswer-based interface, the N-central Administrator Console (NAC), Data Management System (DMS), database, and other core system components. In addition to providing an interface for the probes and agents, the DMS is also the business logic layer of the application. All rules that govern how N-able N-central deals with data are executed at this level. All physical data (configuration or monitored) is stored within the relational PostgreSQL database.
The N-able N-central server is designed and secured so that it may be placed directly on the Internet, however, the recommended best practice is to place it in a restricted internet zone such as a DMZ.
For specific information on the ports that must be accessible for an N-able N-central server, please refer to the Network Requirements page.
What do you want to do?
